how it works
Role-Based
Access Control

Permission Management
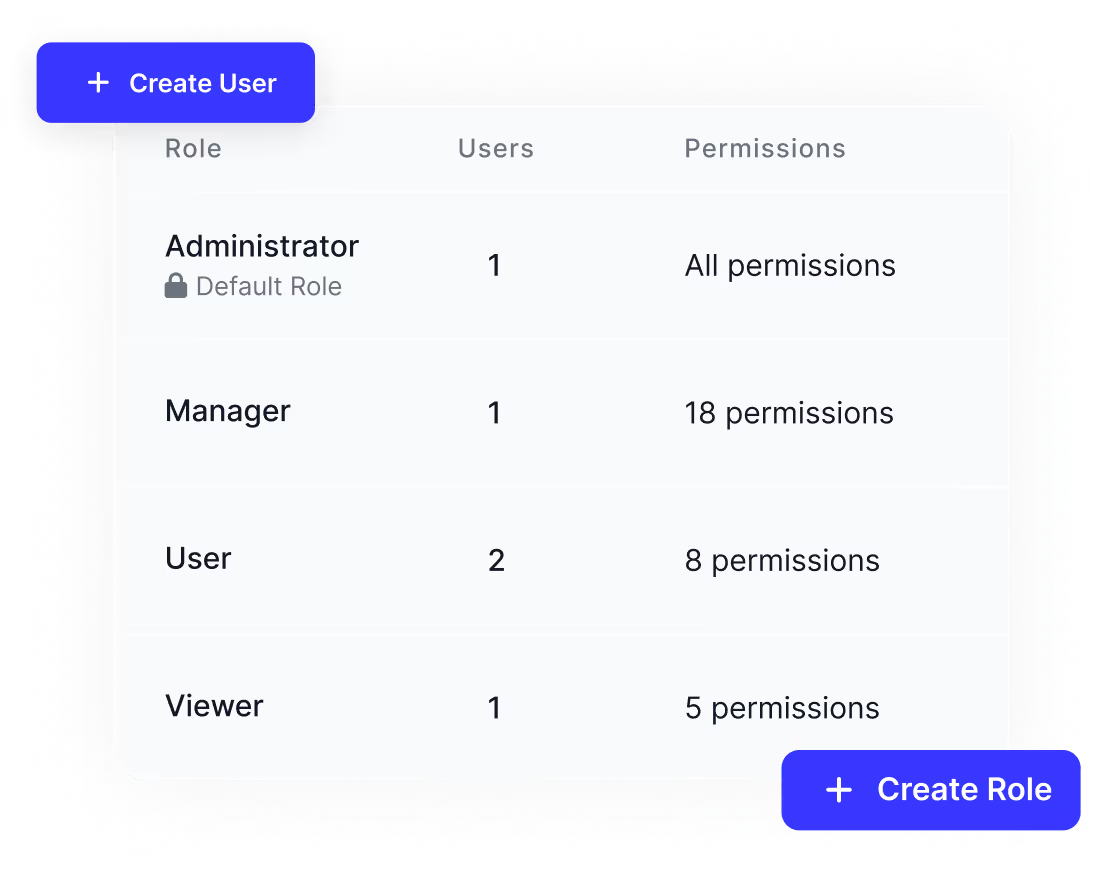
Permissions can be configured at a granular level to control specific actions within the platform. Approval hierarchies and operational boundaries are enforced through configuration. This reduces operational risk and supports separation of duties. Permissions remain transparent and auditable.
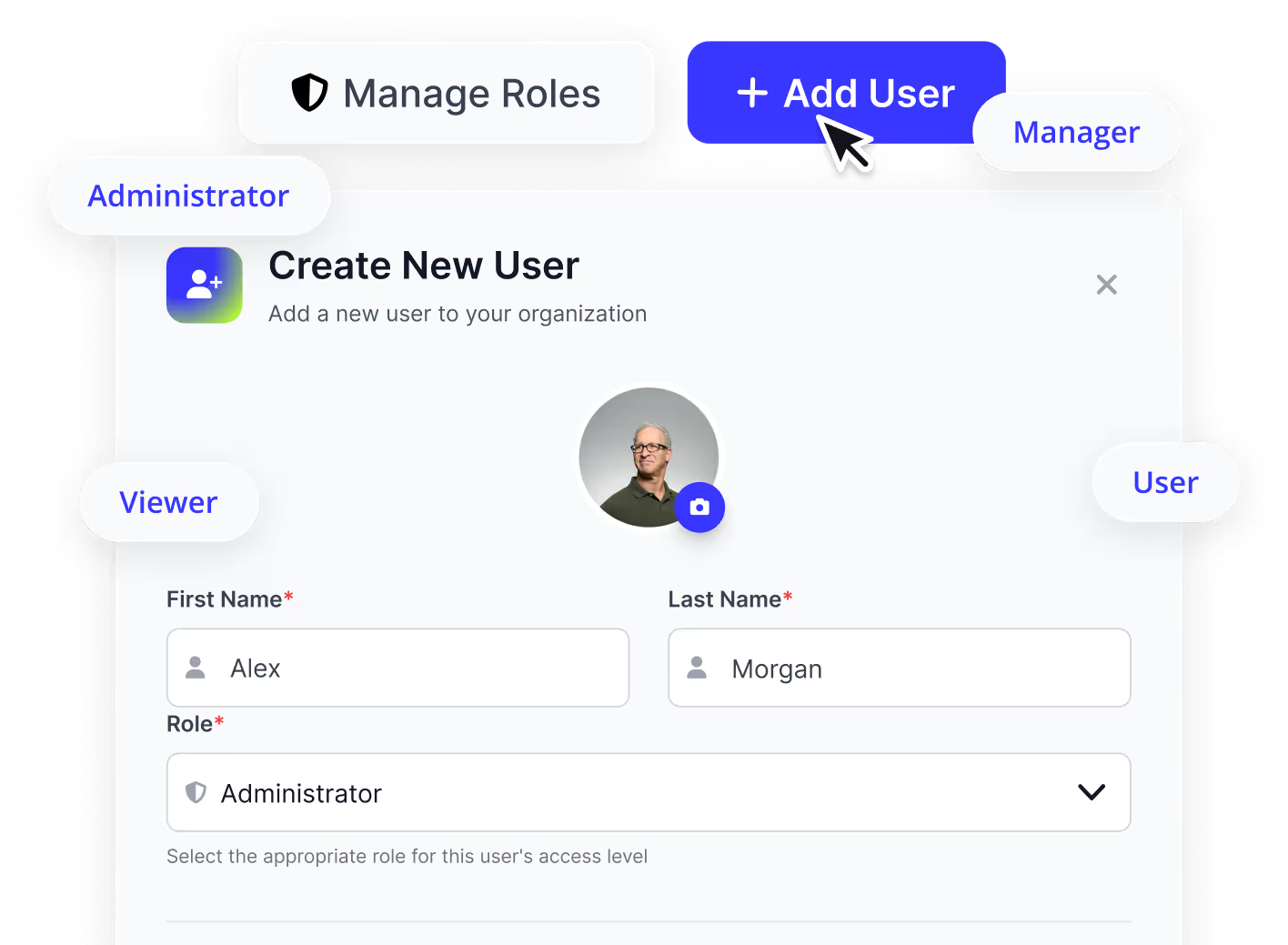
User Lifecycle Management
Manage users throughout their entire lifecycle, from onboarding to deactivation. Roles and permissions can evolve as responsibilities change. All user access is centrally controlled. This simplifies administration while maintaining security.

Granular Role Configuration
Create custom roles tailored to organizational needs across teams and functions. Permissions can span products, workflows, and actions. This enables precise access control without rigid limitations. The model is designed for compliance-driven environments.